 I’ve been using a Bitlocker encrypted drive for a month now and it’s been totally transparent in terms of speed. I’m surprised. I’m also surprised that it was available on my Windows 8.1 (not Pro) OS. Inspired to boost security on my Ultrabook I’ve also enabled secure boot, increased the security level, made sure Defender and Firewall are working and, this is contentious, made sure my login is only via Windows Live account so the password can be changed remotely. Given the reporting and password / device management in the Microsoft Live account though, it seems worth it. Here’s how you can do it too.
I’ve been using a Bitlocker encrypted drive for a month now and it’s been totally transparent in terms of speed. I’m surprised. I’m also surprised that it was available on my Windows 8.1 (not Pro) OS. Inspired to boost security on my Ultrabook I’ve also enabled secure boot, increased the security level, made sure Defender and Firewall are working and, this is contentious, made sure my login is only via Windows Live account so the password can be changed remotely. Given the reporting and password / device management in the Microsoft Live account though, it seems worth it. Here’s how you can do it too.
Not all Ultrabooks (or WIndows 8.1 laptops) without Windows 8.1 Pro will have this feature. Here are the pre-requisites:
- TPM2.0 (You’ll see it in Device Manager)
- Connected Standby. (How to check if you’ve got CS)
- Secure Boot (and it’s turned on in the BIOS)
- Use a Microsoft Live account
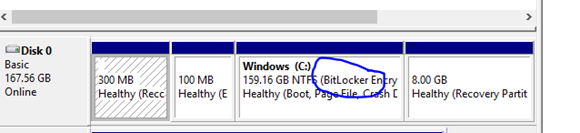
It was so simple on the test device, a Harris Beach developer Ultrabook, that it was funny. Sure enough, looking at the drive manager, it’s now Bitlocker encrypted. Keys are stored online by Microsoft and are accessible through ones Live account.
So If you’ve got a new Ultrabook with Connected Standby (Sony Vaio Duo and a few others right now) the chances are that you’ve got a security feature you didn’t even know about – full disk encryption, BitLocker style.
How do you enable Bitlocker on WIndows 8.1?
Press the Windows key and then type “bitlocker.” You should see this on the top right. Select “Change device encryption settings”

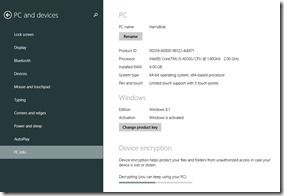
Under PC and Devices –> PC Info you’ll see the Device Encryption option ant the bottom. In the image above you can see I’m actually decrypting a drive (in order to get before and after disc performance figures for you, below) but normally it would be one simple button to turn it on. It takes a while to encrypt the disk (and de-crypt if you turn it off) but you can continue to work while it does that in the background. That’s it!
Bitlocker Performance Impact
AES encryption is done very quickly in hardware on Ultrabooks so there’s no CPU hit. There could be a disk performance hit if your SSD is really fast though. In this case I haven’t noticed any performance hit at all but to fully test that I ran some CrystalDiskMark reports on the SSD, an Intel M.2 SATA SSDSCKGW180A4. Three three results represent the ‘out of the box’ , encrypted and recent unencrypted state.
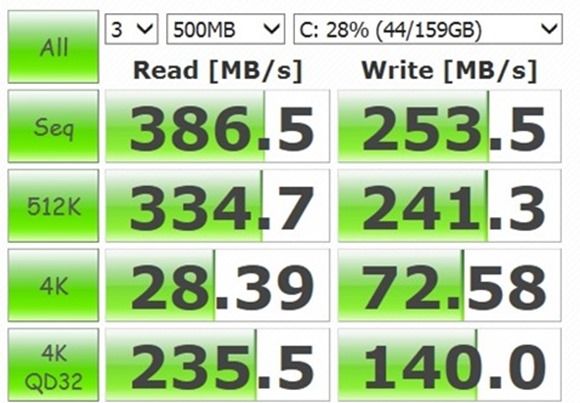
Performance at initial review time, no Bitlocker
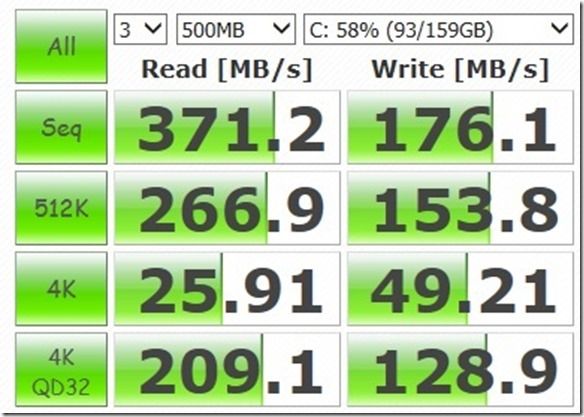
Performance after 1 month with Bitlocker (and a 58% full drive)
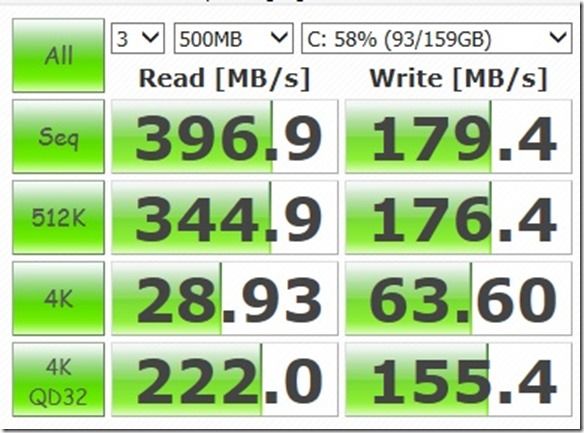
Performance after turning Bitlocker off and decrypting the SSD.
It’s difficult to draw any conclusions apart from that Bitlocker might affect 4K write speeds. Sequential write speeds appear to have dropped simply because the drive is more full. All these are results are good and prove that Bitlocker won’t affect your performance in any significant or noticeable way.
 Other security measures you should consider:
Other security measures you should consider:
- Secure Boot prevents booting from USB sticks, drives etc.
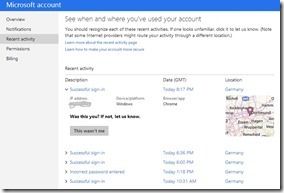
- Use a Microsoft Account – Remote access to password change, login history (see image, right) and control of trusted devices. Remote authentication (two factor for MS accounts.)
- TPM – secure storage of certificates.
Note: Intel Anti-Theft is being dropped. (Not supported after Jan 2015)
Hat-Tip to Arstechnica for the original article that inspired me to test this.






fyi, bitlocker may be transparent on i series processors (I haven’t tried it) but it eats about 1/2 your disk performance on my dell venue 11 pro baytrail. Turned it off and it was like a different machine. Maybe it wouldn’t be an issue with a faster CPU or with a fast SSD instead of eMMC.
So any recent information about if/how full disk encryption affects the life of SSDs and other flash based storage? One thing I know is that from the storage controller’s point of view, it thinks the disk is full and will do whatever special things it does on full disks.
If I encrypt a drive using BitLocker and I can’t boot into Windows or something, can I put the drive into another computer or use a USB adapter and get access to the drive’s contents using some MS tool or built-in OS feature?
Are there ways to boot from a Windows disc or maybe even a Linux Live USB to get access to my files?